This Portfolio Site
Overview
A static portfolio website showcasing my experience, skills, and projects. The site is built with vanilla HTML, CSS, and JavaScript, deployed on AWS using infrastructure-as-code principles with CDK. It demonstrates modern cloud architecture patterns including secure content delivery, automated deployments, and proper SSL/TLS certificate management.
Architecture
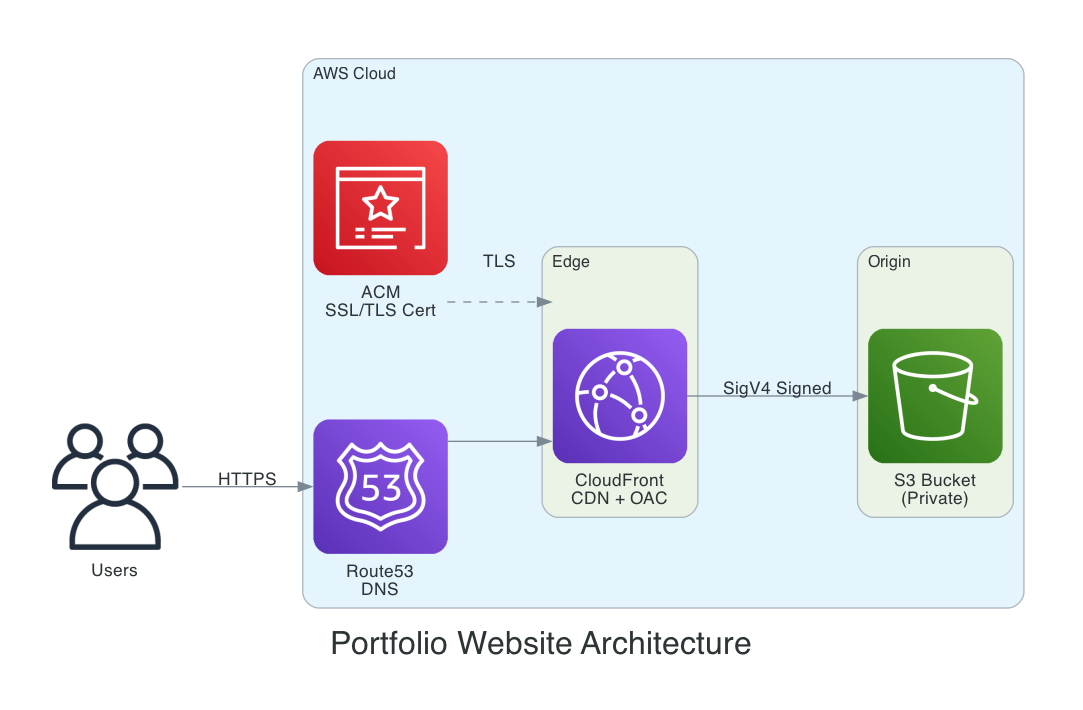
The architecture follows AWS best practices for static website hosting with secure content delivery:
- User Request Flow: DNS resolution through Route53, HTTPS termination at CloudFront with ACM certificate, and secure origin fetch from S3 via Origin Access Control (OAC)
- Security: S3 bucket is private with Block Public Access enabled; CloudFront uses OAC with SigV4 signed requests to access content
CI/CD Pipeline
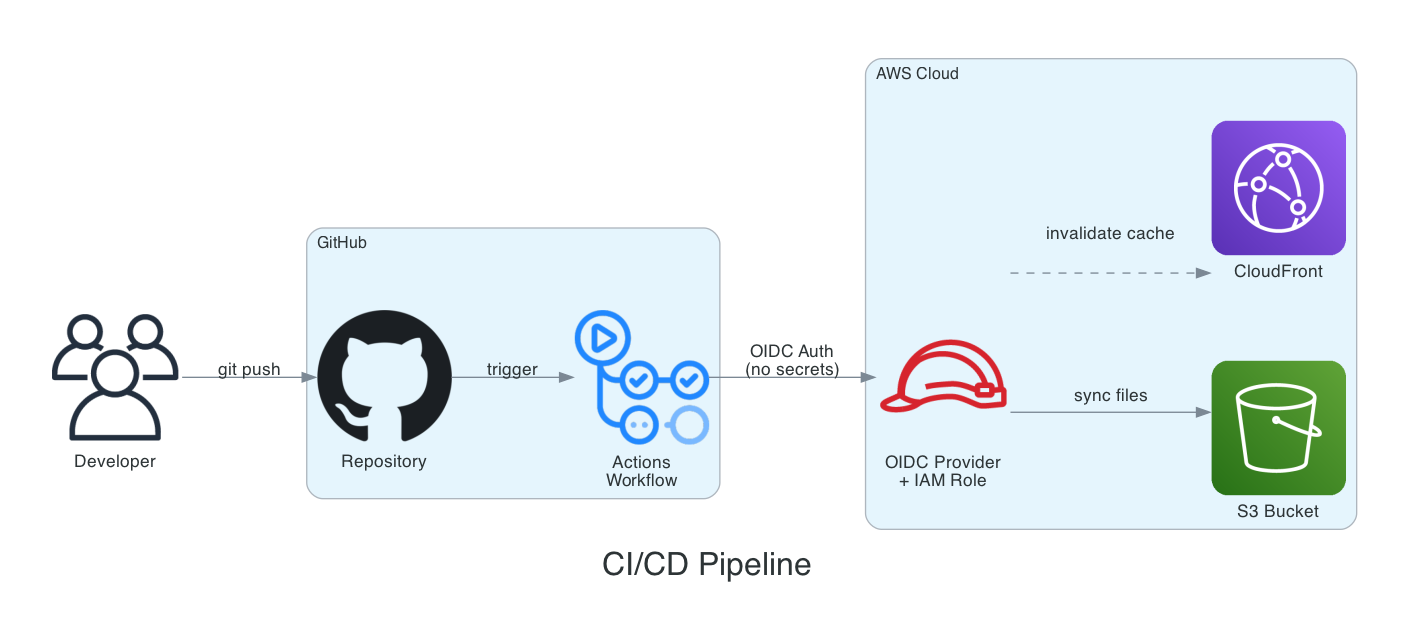
Fully automated deployment pipeline:
- Deployment Flow: Git push triggers GitHub Actions, which authenticates via OIDC (no long-lived credentials) to deploy files to S3 and invalidate the CloudFront cache
- Security: OIDC federation eliminates the need for stored AWS credentials; IAM role has scoped permissions for S3 and CloudFront operations only
Architecture Decisions
OAC over OAI
Decision: Use Origin Access Control instead of Origin Access Identity
Rationale: OAI is deprecated by AWS. OAC provides better security with support for all S3 features including SSE-KMS encryption, and works with all AWS regions. It also supports AWS Signature Version 4, which is required for newer regions.
CDK over CloudFormation/Console
Decision: Use AWS CDK (TypeScript) for infrastructure management
Rationale: CDK provides type safety, IDE autocomplete, and the ability to use programming constructs like loops and conditionals. Infrastructure changes are version controlled and reviewable. The same patterns can be reused across multiple projects.
CloudFront over Direct S3
Decision: Serve content through CloudFront rather than S3 website hosting
Rationale: CloudFront enables HTTPS with custom domain (S3 website endpoints don't support HTTPS), provides global edge caching for better performance, and allows the S3 bucket to remain private. Cache invalidation ensures updates are immediately visible.
OIDC over IAM Access Keys
Decision: Use OpenID Connect for GitHub Actions authentication
Rationale: No long-lived credentials to manage or rotate. Tokens are short-lived and scoped to specific workflows. This follows AWS security best practices and eliminates the risk of leaked access keys.
Tech Stack
S3
Static file storage with versioning enabled
CloudFront
Global CDN with edge caching
Route53
DNS management and routing
ACM
SSL/TLS certificate management
CDK
Infrastructure as code (TypeScript)
GitHub Actions
CI/CD pipeline automation
CI/CD Pipeline
The deployment pipeline is fully automated using GitHub Actions:
- Trigger: Push to main branch or manual workflow dispatch
- Authentication: OIDC federation with AWS (no stored credentials)
- Build: Any preprocessing (currently minimal for static site)
- Deploy: Sync files to S3 bucket with appropriate cache headers
- Invalidate: Create CloudFront invalidation for immediate updates
Average deployment time is under 2 minutes from push to live.
Related Blog Post
Technical deep dive inspired by a misconfiguration in this site's redirect setup and the modern solution:
2 Buckets 1 Website: How CloudFront Changes AWS Static Site Redirects →Source Code
Explore the full codebase, including CDK infrastructure and CI/CD pipeline:
lifeunsubscribe/resume-website on GitHub →